Secure Workplace
In our overview, you will find the most important security tips for your work environment. Just click on the headlines to read more.

Secure work computer
- Protect your computer with a secure password
- Lock your computer when leaving your desk (press the Windows key + L)
- Encrypt the hard drive of your computer so that others are unable to access the information stored on your device in case you lose it.
- The administrator’s account should not be the standard account for working on your computer.
- Please keep our tips for the secure handling of external storage devices (e.g. USB sticks) in mind
- Make sure that there is a backup of important data
- Install updates as soon as they are available, since attackers are known to directly exploit any security gaps
- Scan your system regularly and if you suspect a security issue with a virus scanner
- Keep the minimization principle in mind to reduce potential damage

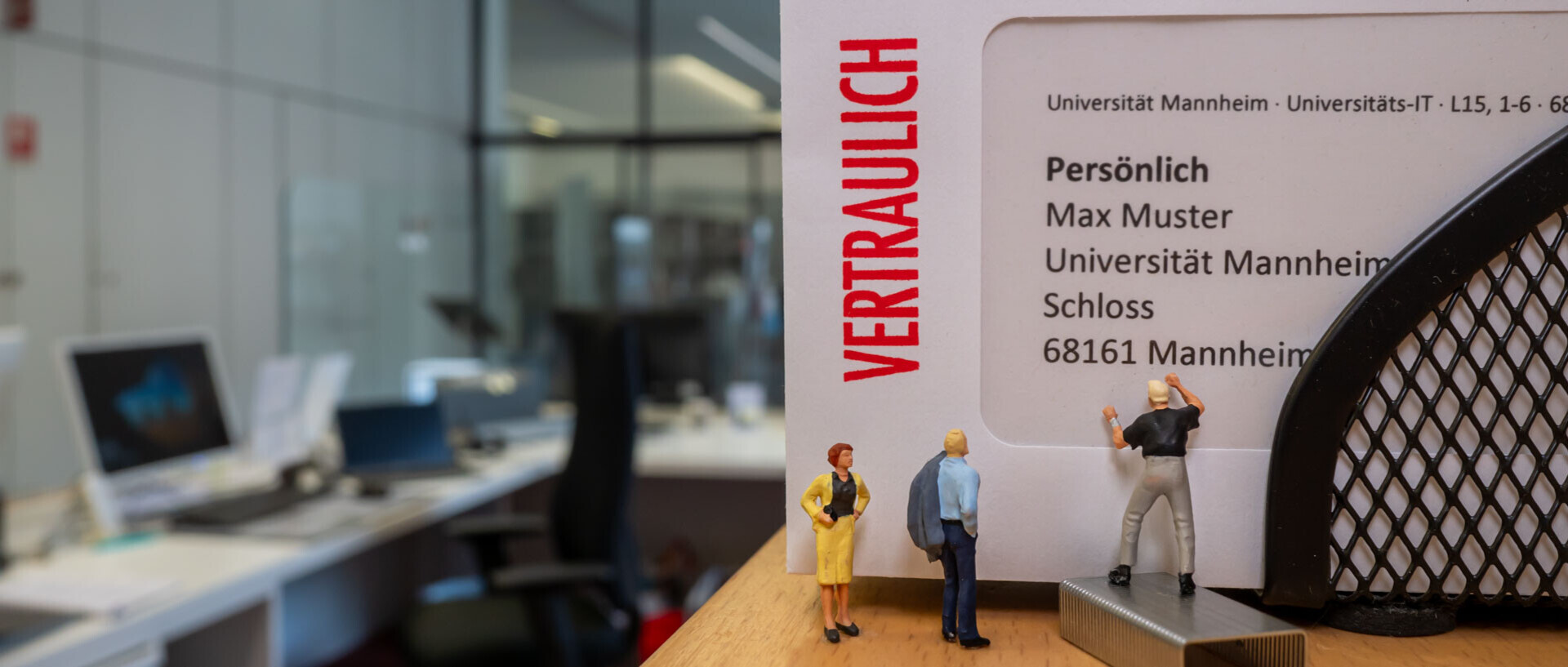
Secure workplace
- Close the doors and windows of your room, when you leave the room. Doors should be locked, if possible.
- Arrange your screens and documents in a way that third parties (other family members, room mates or strangers) are unable to see your screen and documents. If this is not possible, please use a privacy screen.
- If documents and external storage devices (e.g., USB sticks) are not in use, they should not be left on the desk and should be locked away.
- Please make sure that the office space is not entered by unauthorized third parties.

What to observe when working outside of the university buildings
- In public spaces, work devices, documents and external storage devices must be observed at all times, in particular on your way between two work locations.
- You should never dispose of confidential or sensitive documents and data carriers in your house waste bins but always in the special bins designated for this purpose at the university.
- Telephone calls about confidential topics should only be made in separate rooms and not on balconies or outside.
- Please refrain from using printers outside of the university, unless this is absolutely necessary.
For more information on the various information security topics, please read our security tips.
Further information
Secure backup
Make sure you back up your files regularly. You should always store your files on the network drive (file service) of the University of Mannheim and not on your work computer. We regularly back up all files that you store on the file service and your data are protected against loss.
If you want to have another, additional back up of your data, you can store the files encrypted on a USB stick or an external hard drive of the university. Please note our information on the secure handling of external storage devices, such as USB sticks.
Handling external storage devices (e.g., USB sticks)
Protect against third-party access
USB sticks, external hard drives and other external storage media can be easily lost. In order to prevent third parties from accessing the data stored on these devices, you should encrypt your files before storing them on such storage devices. Select one of three encryption methods for external storage devices. If you do not use the external storage devices, you should lock them away in order to protect them against third-party access.
Deletion not possible
There are various free programs to restore files that seem to have been deleted within only a few seconds. Encrypting the files helps to prevent unauthorized person from using restored data.
Have you already stored unencrypted, sensitive data on an external data carrier?
Just overwrite the device several times with uncritical data. This makes it more difficult to restore older files. Since this does not always work out, you should use the special bins designated for this purpose to dispose of this storage device.
Administrator’s accounts and user accounts
Working with the admin account should not be the default. Please use a user account without admin rights for your regular work. This applies to your operating system and to each program that you use.
Admin rights are risky
If a virus tries to spread on your computer, the chances of success depend on the account type you use. If you work with a regular user account, the spread of the malicious software is limited. If you use the admin account as default account, the virus can spread more widely and cause more damage.
Separate accounts offer protection
- You use a user account without admin rights for your daily work.
- The admin account is only used for administrative tasks such as installing programs.
Setting up a user account
If you do not yet have an administrator’s account and a user account, you should set up a user account as soon as possible to protect your data. You can use the Microsoft instructions or contact your administrator and/
or the Premium Support or IT support. Minimization principle
The minimization principle is easy to explain: As little as possible as much as necessary!
This principle can be applied to almost every area to reduce possible damage. Here are a few examples:
- Only install the programs you absolutely need for working. Programs may contain errors that attackers can use to infect your computer with malicious software or to spy on you. Less programs on your computer mean less danger for you.
- Always work with as little rights as possible. When it comes to your daily work, this refers to your operating system, for example. For more information, please refer to the section administrator’s account and user account. If your account has limited rights, this also limits the damage, no matter if the damage is caused unintenionally or through third parties.
- Always ask yourself why the other person wants this information and to which extent this person needs the information, before you forward the information. Only forward the information required. This corresponds to the principle of data minimization and may also prevent a personal data breach.
Safe disposal of appliances (laptop)
- Documents can be disposed of in the data security container.
- To dispose IT equipment and hard disks, fill out the IT disposal application form provided by the department of procurement. When disposing appliances, ensure that all data is reliably deleted. You can find instructions for deletion here: https://www.uni-mannheim.de/en/it/instructions/hard-drives-and-ssds/